Chapter 45: Synthesis — From Al-Kindi to Post-Quantum#
This final chapter synthesises the entire arc of Elements of Cryptanalysis. We trace the discipline from its origins in ninth-century Baghdad to the post-quantum frontier, drawing out the recurring patterns, key themes, and open problems that define the field today.
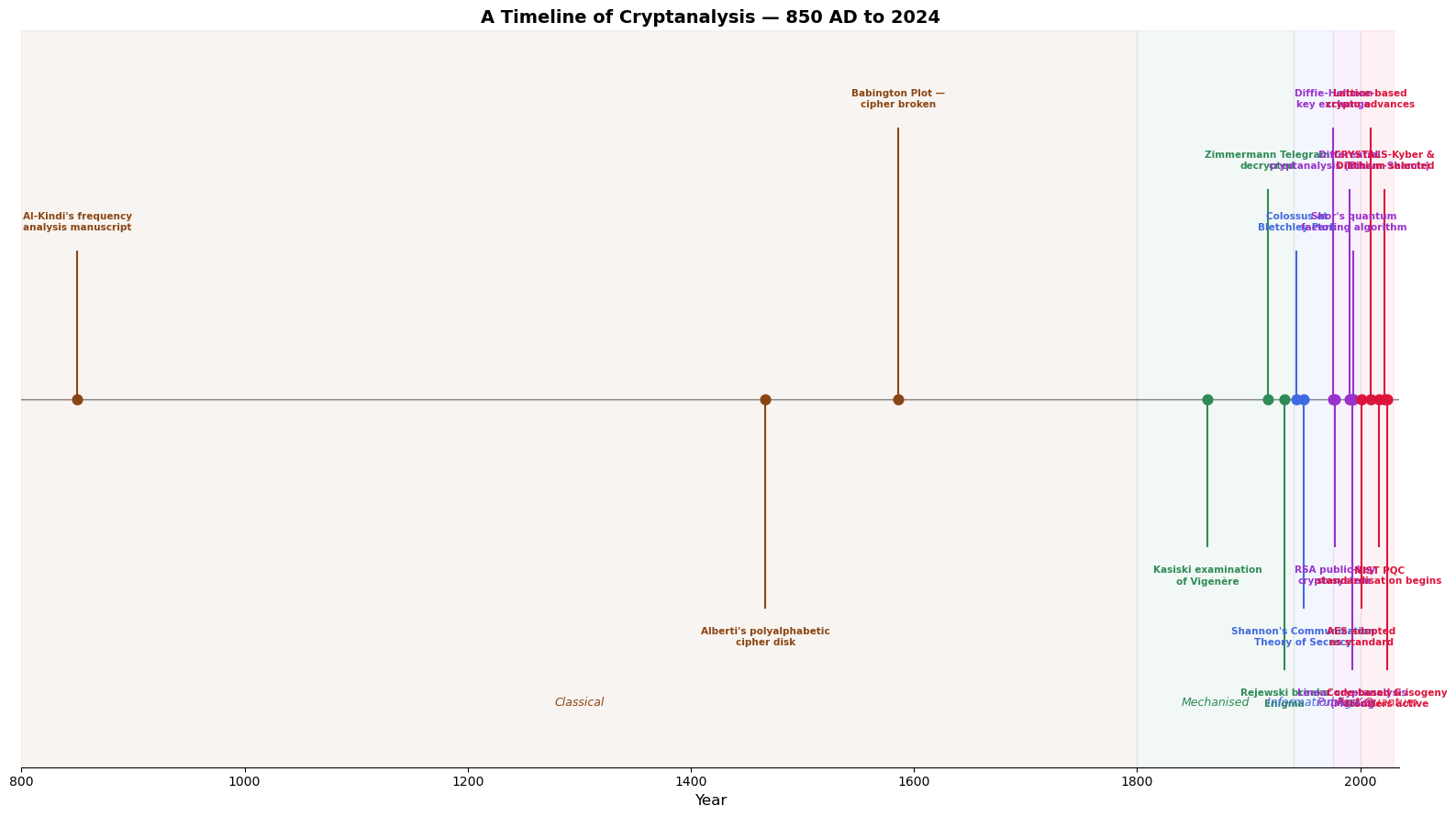
45.1 A Timeline of Cryptanalysis (850 AD – 2024)#
Cryptanalysis has evolved through several distinct eras. The visualisation below places landmark events on a logarithmic-feel timeline that compresses the long pre-modern period while expanding the rapid developments of the twentieth and twenty-first centuries.
Show code cell source
import numpy as np
import matplotlib.pyplot as plt
# --- Landmark events in the history of cryptanalysis ---
events = [
(850, "Al-Kindi's frequency\nanalysis manuscript"),
(1467, "Alberti's polyalphabetic\ncipher disk"),
(1586, "Babington Plot —\ncipher broken"),
(1863, "Kasiski examination\nof Vigenère"),
(1917, "Zimmermann Telegram\ndecrypted"),
(1932, "Rejewski breaks\nEnigma"),
(1943, "Colossus at\nBletchley Park"),
(1949, "Shannon's Communication\nTheory of Secrecy"),
(1976, "Diffie-Hellman\nkey exchange"),
(1977, "RSA public-key\ncryptosystem"),
(1990, "Differential\ncryptanalysis (Biham-Shamir)"),
(1993, "Linear cryptanalysis\n(Matsui)"),
(1994, "Shor's quantum\nfactoring algorithm"),
(2001, "AES adopted\nas standard"),
(2009, "Lattice-based\ncrypto advances"),
(2017, "NIST PQC\nstandardisation begins"),
(2022, "CRYSTALS-Kyber &\nDilithium selected"),
(2024, "Code-based & isogeny\nfrontiers active"),
]
years = [e[0] for e in events]
labels = [e[1] for e in events]
fig, ax = plt.subplots(figsize=(16, 9))
# Colour-code by era
colours = []
for y in years:
if y < 1800:
colours.append('#8B4513') # Classical era — brown
elif y < 1940:
colours.append('#2E8B57') # Early modern — green
elif y < 1976:
colours.append('#4169E1') # Mid-century — blue
elif y < 2000:
colours.append('#9932CC') # Public-key era — purple
else:
colours.append('#DC143C') # Post-quantum era — crimson
# Plot stems
for i, (y, lbl) in enumerate(events):
side = 1 if i % 2 == 0 else -1
height = side * (0.6 + 0.25 * (i % 3))
ax.plot([y, y], [0, height], color=colours[i], linewidth=1.5, zorder=2)
ax.scatter(y, 0, color=colours[i], s=60, zorder=3)
ax.text(y, height + side * 0.08, lbl, ha='center',
va='bottom' if side > 0 else 'top',
fontsize=7.5, color=colours[i], fontweight='bold')
# Central axis
ax.axhline(0, color='grey', linewidth=1.0, zorder=1)
# Era shading
era_spans = [
(800, 1800, '#8B4513', 'Classical'),
(1800, 1940, '#2E8B57', 'Mechanised'),
(1940, 1976, '#4169E1', 'Information Age'),
(1976, 2000, '#9932CC', 'Public-Key'),
(2000, 2030, '#DC143C', 'Post-Quantum'),
]
for start, end, col, name in era_spans:
ax.axvspan(start, end, alpha=0.06, color=col)
ax.text((start + end) / 2, -1.25, name, ha='center', fontsize=9,
color=col, fontstyle='italic')
ax.set_xlim(800, 2035)
ax.set_ylim(-1.5, 1.5)
ax.set_xlabel('Year', fontsize=12)
ax.set_title('A Timeline of Cryptanalysis — 850 AD to 2024',
fontsize=14, fontweight='bold')
ax.set_yticks([])
ax.spines['left'].set_visible(False)
ax.spines['right'].set_visible(False)
ax.spines['top'].set_visible(False)
plt.tight_layout()
plt.savefig('fig_ch45_timeline.png', dpi=150, bbox_inches='tight')
plt.show()
Historical Note
Al-Kindi’s Risalah fi Istikhraj al-Mu’amma (c. 850 AD) is the earliest known treatise on cryptanalysis. His frequency-analysis technique remained the dominant attack strategy for over 600 years — an extraordinary reign in any technical discipline.
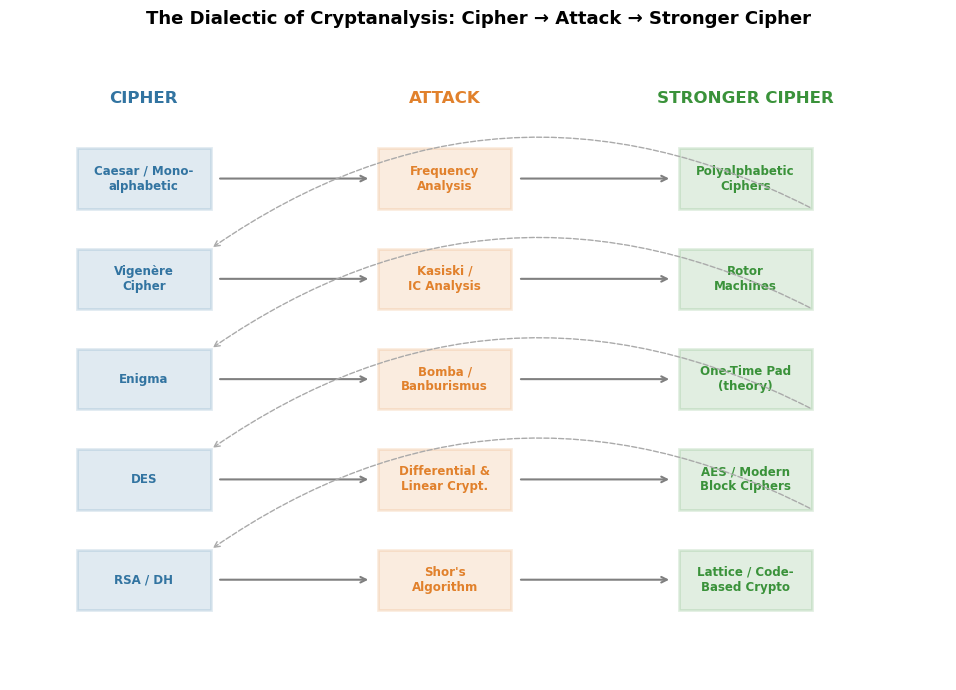
45.2 The Recurring Pattern: Cipher → Attack → Stronger Cipher#
Throughout the history of cryptography, a single dialectical pattern has repeated itself with striking regularity:
A cipher is proposed, believed secure.
An attack reveals a structural weakness.
A stronger cipher is designed in response, informed by the nature of the attack.
This evolutionary arms race is the engine that drives cryptographic progress.
Show code cell source
import numpy as np
import matplotlib.pyplot as plt
# Cipher-Attack-Response triples
triples = [
('Caesar / Mono-\nalphabetic', 'Frequency\nAnalysis', 'Polyalphabetic\nCiphers'),
('Vigenère\nCipher', 'Kasiski /\nIC Analysis', 'Rotor\nMachines'),
('Enigma', 'Bomba /\nBanburismus', 'One-Time Pad\n(theory)'),
('DES', 'Differential &\nLinear Crypt.', 'AES / Modern\nBlock Ciphers'),
('RSA / DH', "Shor's\nAlgorithm", 'Lattice / Code-\nBased Crypto'),
]
fig, ax = plt.subplots(figsize=(14, 7))
n = len(triples)
y_positions = np.arange(n)[::-1] * 1.5
box_w = 2.0
col_cipher = 0.0
col_attack = 4.5
col_response = 9.0
cipher_color = '#3274A1'
attack_color = '#E1812C'
response_color = '#3A923A'
for i, (cipher, attack, response) in enumerate(triples):
y = y_positions[i]
# Boxes
for x, label, color in [(col_cipher, cipher, cipher_color),
(col_attack, attack, attack_color),
(col_response, response, response_color)]:
rect = plt.Rectangle((x - box_w/2, y - 0.45), box_w, 0.9,
facecolor=color, alpha=0.15, edgecolor=color,
linewidth=2, zorder=2)
ax.add_patch(rect)
ax.text(x, y, label, ha='center', va='center', fontsize=8.5,
fontweight='bold', color=color, zorder=3)
# Arrows
ax.annotate('', xy=(col_attack - box_w/2 - 0.1, y),
xytext=(col_cipher + box_w/2 + 0.1, y),
arrowprops=dict(arrowstyle='->', color='grey', lw=1.5))
ax.annotate('', xy=(col_response - box_w/2 - 0.1, y),
xytext=(col_attack + box_w/2 + 0.1, y),
arrowprops=dict(arrowstyle='->', color='grey', lw=1.5))
# Feedback loop (response feeds next cipher)
if i < n - 1:
y_next = y_positions[i + 1]
ax.annotate('', xy=(col_cipher + box_w/2, y_next + 0.45),
xytext=(col_response + box_w/2, y - 0.45),
arrowprops=dict(arrowstyle='->', color='#AAAAAA',
lw=1.0, linestyle='--',
connectionstyle='arc3,rad=0.3'))
# Column headers
header_y = y_positions[0] + 1.2
for x, label, color in [(col_cipher, 'CIPHER', cipher_color),
(col_attack, 'ATTACK', attack_color),
(col_response, 'STRONGER CIPHER', response_color)]:
ax.text(x, header_y, label, ha='center', va='center', fontsize=12,
fontweight='bold', color=color)
ax.set_xlim(-2, 12)
ax.set_ylim(-1.5, header_y + 0.8)
ax.set_aspect('equal')
ax.axis('off')
ax.set_title('The Dialectic of Cryptanalysis: Cipher → Attack → Stronger Cipher',
fontsize=13, fontweight='bold', pad=15)
plt.tight_layout()
plt.savefig('fig_ch45_dialectic.png', dpi=150, bbox_inches='tight')
plt.show()
Key Insight
Every successful attack has made cryptography stronger, not weaker. Differential cryptanalysis did not destroy block ciphers — it led to the design of AES with provable resistance to such attacks. Shor’s algorithm has not destroyed public-key cryptography — it has catalysed the development of post-quantum schemes.
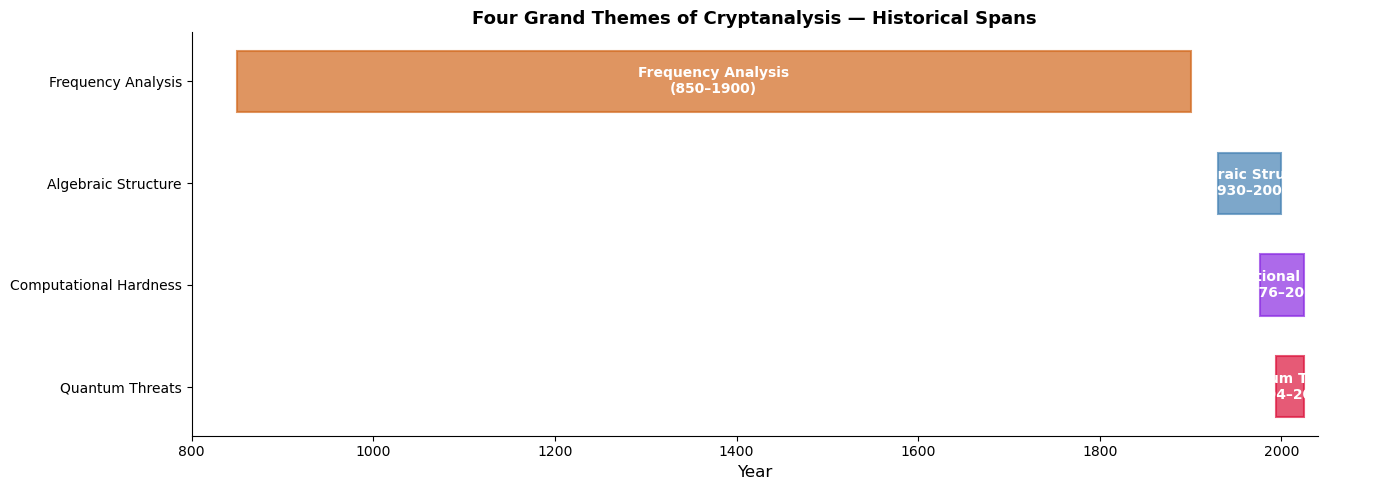
45.3 Key Themes Across the Course#
Four grand themes emerge from our study:
Theme |
Era |
Central Idea |
|---|---|---|
Frequency Analysis |
Classical (850–1800s) |
Natural-language statistics reveal plaintext |
Algebraic Structure |
Mechanical/Modern (1930s–1990s) |
Exploiting mathematical structure in ciphers |
Computational Hardness |
Public-Key (1976–present) |
Security rests on presumed intractable problems |
Quantum Threats |
Post-Quantum (1994–present) |
Quantum computers break hardness assumptions |
Show code cell source
import numpy as np
import matplotlib.pyplot as plt
# Visualise the four key themes as overlapping historical bands
themes = [
('Frequency Analysis', 850, 1900, '#D2691E'),
('Algebraic Structure', 1930, 2000, '#4682B4'),
('Computational Hardness', 1976, 2025, '#8A2BE2'),
('Quantum Threats', 1994, 2025, '#DC143C'),
]
fig, ax = plt.subplots(figsize=(14, 5))
for i, (name, start, end, color) in enumerate(themes):
y = i
ax.barh(y, end - start, left=start, height=0.6, color=color, alpha=0.7,
edgecolor=color, linewidth=1.5)
# Label inside bar
mid = (start + end) / 2
ax.text(mid, y, f'{name}\n({start}–{end})', ha='center', va='center',
fontsize=10, fontweight='bold', color='white')
ax.set_yticks(range(len(themes)))
ax.set_yticklabels([t[0] for t in themes], fontsize=10)
ax.set_xlabel('Year', fontsize=12)
ax.set_title('Four Grand Themes of Cryptanalysis — Historical Spans',
fontsize=13, fontweight='bold')
ax.set_xlim(800, 2040)
ax.invert_yaxis()
ax.spines['top'].set_visible(False)
ax.spines['right'].set_visible(False)
plt.tight_layout()
plt.savefig('fig_ch45_themes.png', dpi=150, bbox_inches='tight')
plt.show()
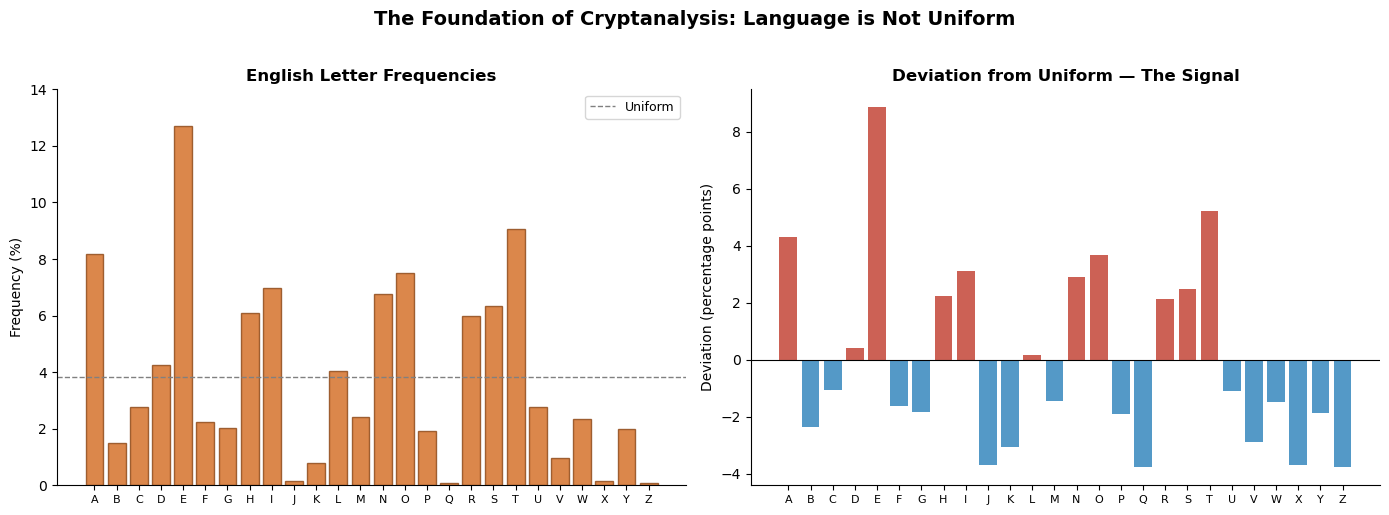
45.3.1 Theme 1: Frequency Analysis#
The insight that human language is not uniform — that certain letters, digrams, and patterns recur with predictable frequencies — was the first great weapon of the cryptanalyst. Al-Kindi formalised it, and it remained dominant for centuries. Even modern attacks on stream ciphers echo this idea: any deviation from uniform randomness is a potential vulnerability.
Show code cell source
import numpy as np
import matplotlib.pyplot as plt
# English letter frequencies (approximate)
letters = list('ABCDEFGHIJKLMNOPQRSTUVWXYZ')
english_freq = np.array([
8.167, 1.492, 2.782, 4.253, 12.702, 2.228, 2.015, 6.094, 6.966,
0.153, 0.772, 4.025, 2.406, 6.749, 7.507, 1.929, 0.095, 5.987,
6.327, 9.056, 2.758, 0.978, 2.360, 0.150, 1.974, 0.074
])
uniform = np.ones(26) * (100.0 / 26)
fig, axes = plt.subplots(1, 2, figsize=(14, 5))
# English frequencies
axes[0].bar(letters, english_freq, color='#D2691E', alpha=0.8, edgecolor='#8B4513')
axes[0].axhline(100/26, color='grey', linestyle='--', linewidth=1, label='Uniform')
axes[0].set_title('English Letter Frequencies', fontsize=12, fontweight='bold')
axes[0].set_ylabel('Frequency (%)', fontsize=10)
axes[0].legend(fontsize=9)
axes[0].set_ylim(0, 14)
# Deviation from uniform — the cryptanalyst's signal
deviation = english_freq - uniform
colors = ['#C0392B' if d > 0 else '#2980B9' for d in deviation]
axes[1].bar(letters, deviation, color=colors, alpha=0.8)
axes[1].axhline(0, color='black', linewidth=0.8)
axes[1].set_title('Deviation from Uniform — The Signal', fontsize=12, fontweight='bold')
axes[1].set_ylabel('Deviation (percentage points)', fontsize=10)
for ax in axes:
ax.spines['top'].set_visible(False)
ax.spines['right'].set_visible(False)
ax.tick_params(axis='x', labelsize=8)
fig.suptitle('The Foundation of Cryptanalysis: Language is Not Uniform',
fontsize=14, fontweight='bold', y=1.02)
plt.tight_layout()
plt.savefig('fig_ch45_frequency.png', dpi=150, bbox_inches='tight')
plt.show()
45.3.2 Theme 2: Algebraic Structure#
The twentieth century brought the realisation that ciphers are mathematical objects whose structure can be analysed algebraically. Rejewski modelled the Enigma permutations as group elements. Differential and linear cryptanalysis exploit the algebraic properties of S-boxes. The shift from “art” to “science” in cryptanalysis was, at its heart, the shift toward algebraic thinking.
45.3.3 Theme 3: Computational Hardness#
With the advent of public-key cryptography in 1976, security became explicitly linked to computational hardness assumptions: integer factorisation, discrete logarithms, and later lattice problems. The cryptanalyst’s task transformed from finding the key to finding an efficient algorithm for a hard problem — or proving that none exists.
45.3.4 Theme 4: Quantum Threats#
Shor’s 1994 algorithm demonstrated that quantum computers could efficiently solve factoring and discrete logarithms — the very problems underpinning RSA, DSA, and elliptic curve cryptography. This existential threat has driven the development of post-quantum cryptography based on lattices, codes, hash functions, isogenies, and multivariate equations.
Show code cell source
import numpy as np
import matplotlib.pyplot as plt
# Comparative complexity: classical vs quantum for key cryptographic problems
problems = [
'Integer\nFactoring',
'Discrete\nLogarithm',
'Elliptic Curve\nDL',
'Lattice\nSVP',
'Syndrome\nDecoding',
'Hash\nPreimage',
]
# Exponents: complexity ~ O(2^exponent) for n-bit security parameter
# Rough illustrative values for n=256
classical_exp = np.array([64, 64, 128, 128, 128, 256]) # sub-exponential or exponential
quantum_exp = np.array([1, 1, 1, 90, 85, 128]) # Shor: poly; Grover: sqrt
x = np.arange(len(problems))
width = 0.35
fig, ax = plt.subplots(figsize=(12, 6))
bars1 = ax.bar(x - width/2, classical_exp, width, label='Best Classical Attack',
color='#4682B4', alpha=0.8, edgecolor='#2C5F8A')
bars2 = ax.bar(x + width/2, quantum_exp, width, label='Best Quantum Attack',
color='#DC143C', alpha=0.8, edgecolor='#A01030')
# Highlight broken problems
for i in range(3):
ax.text(x[i] + width/2, quantum_exp[i] + 3, 'BROKEN', ha='center',
fontsize=8, fontweight='bold', color='#DC143C')
# Highlight quantum-resistant problems
for i in range(3, 6):
ax.text(x[i] + width/2, quantum_exp[i] + 3, 'Resistant', ha='center',
fontsize=8, fontweight='bold', color='#2E8B57')
ax.set_xticks(x)
ax.set_xticklabels(problems, fontsize=9)
ax.set_ylabel('Effective Security (log$_2$ operations)', fontsize=11)
ax.set_title('Classical vs Quantum Attack Complexity (n = 256 bits)',
fontsize=13, fontweight='bold')
ax.legend(fontsize=10, loc='upper left')
ax.set_ylim(0, 280)
ax.axhline(128, color='green', linestyle='--', linewidth=1, alpha=0.5,
label='128-bit security threshold')
ax.spines['top'].set_visible(False)
ax.spines['right'].set_visible(False)
plt.tight_layout()
plt.savefig('fig_ch45_quantum_vs_classical.png', dpi=150, bbox_inches='tight')
plt.show()
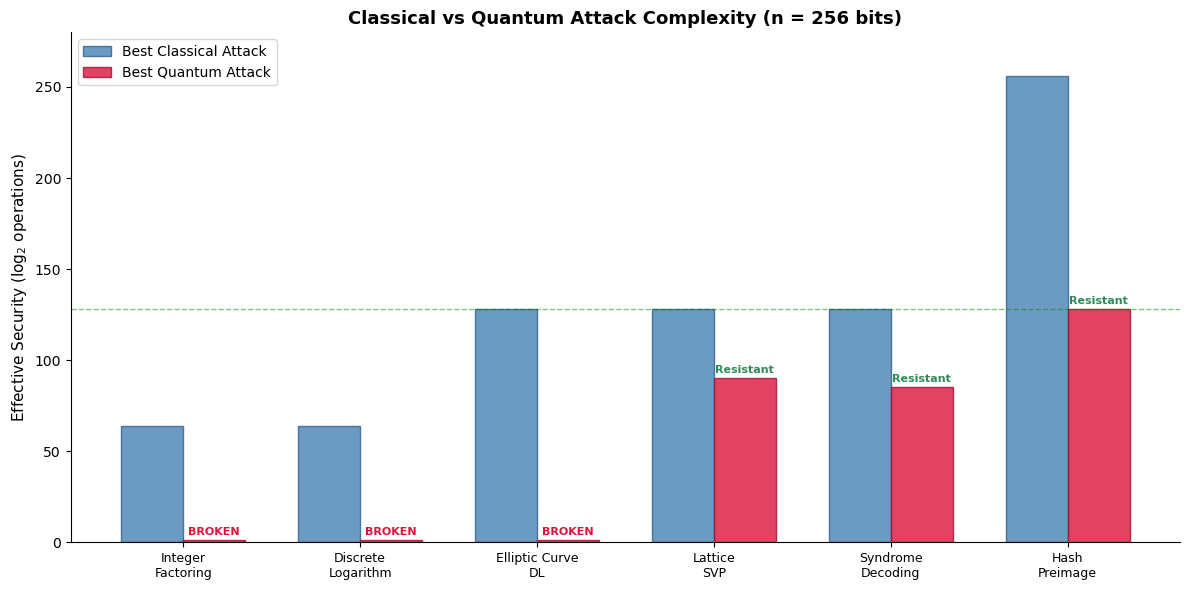
Why Post-Quantum Matters Now
Even though large-scale quantum computers do not yet exist, the “harvest now, decrypt later” threat means that adversaries can store encrypted traffic today and decrypt it once quantum computers become available. Migration to post-quantum cryptography is therefore urgent.
45.4 Open Problems in Cryptanalysis#
The field remains vibrantly open. Below we catalogue the most significant unsolved questions, organised by domain.
Show code cell source
import numpy as np
import matplotlib.pyplot as plt
# Open problems organised by area with estimated difficulty/impact
areas = [
'Lattice\nSecurity',
'Code-Based\nCrypto',
'Symmetric\nCiphers',
'Quantum\nAlgorithms',
'Complexity\nTheory',
'Side-Channel\nAttacks',
]
open_problems = [
'Tighter LWE hardness\nreductions',
'Efficient decoding of\nrandom linear codes',
'Provable security of\nAES against all attacks',
'Quantum advantage for\nlattice problems?',
'P vs NP and\none-way functions',
'Formal verification of\nleakage resilience',
]
# Impact score (subjective, 1–10)
impact = np.array([9, 7, 8, 10, 10, 6])
# Difficulty score (subjective, 1–10)
difficulty = np.array([7, 6, 9, 9, 10, 5])
fig, ax = plt.subplots(figsize=(10, 8))
colours = ['#4682B4', '#2E8B57', '#D2691E', '#DC143C', '#9932CC', '#FF8C00']
scatter = ax.scatter(difficulty, impact, s=800, c=colours, alpha=0.7,
edgecolors='black', linewidths=1.5, zorder=3)
for i in range(len(areas)):
ax.annotate(f'{areas[i]}\n\n{open_problems[i]}',
(difficulty[i], impact[i]),
ha='center', va='center', fontsize=7,
fontweight='bold', color='white', zorder=4)
ax.set_xlabel('Estimated Difficulty', fontsize=12)
ax.set_ylabel('Potential Impact', fontsize=12)
ax.set_title('Open Problems in Cryptanalysis — Difficulty vs Impact',
fontsize=13, fontweight='bold')
ax.set_xlim(3.5, 11)
ax.set_ylim(4.5, 11)
ax.spines['top'].set_visible(False)
ax.spines['right'].set_visible(False)
ax.grid(True, alpha=0.3)
plt.tight_layout()
plt.savefig('fig_ch45_open_problems.png', dpi=150, bbox_inches='tight')
plt.show()
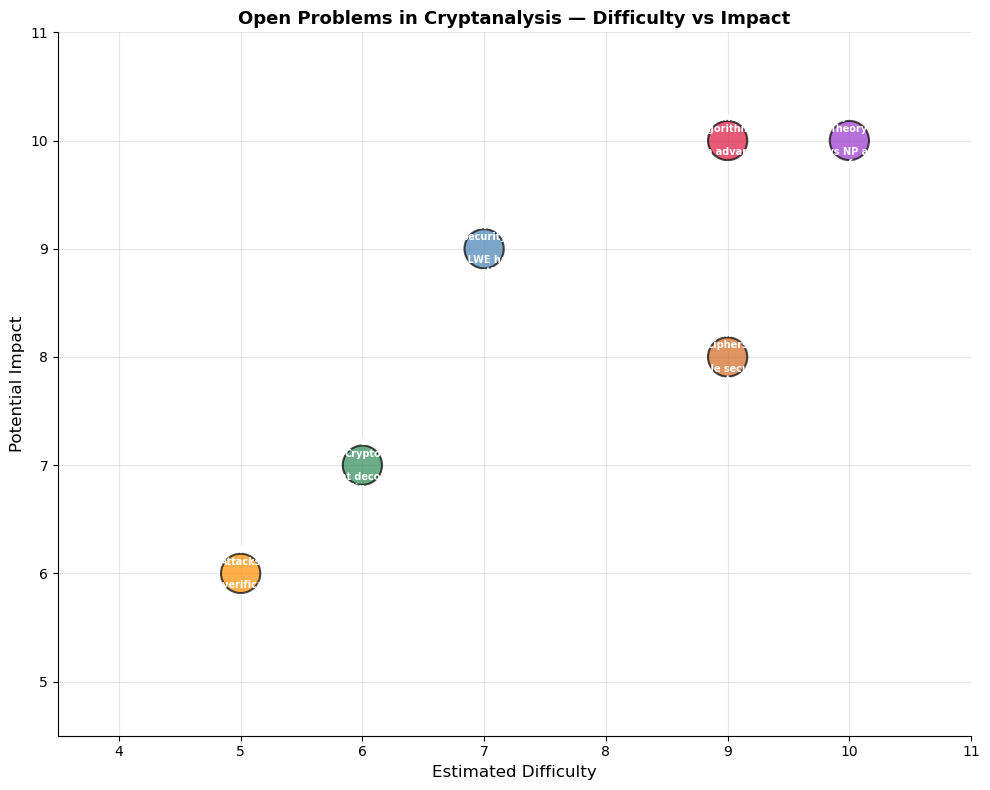
The Deepest Open Problem
The question of whether one-way functions exist — intimately connected to the P vs NP problem — remains the deepest open question in cryptography. If P = NP, then no computationally-secure cryptography is possible (except information-theoretic schemes like the one-time pad). Nearly all of modern cryptography rests on the assumption that P ≠ NP.
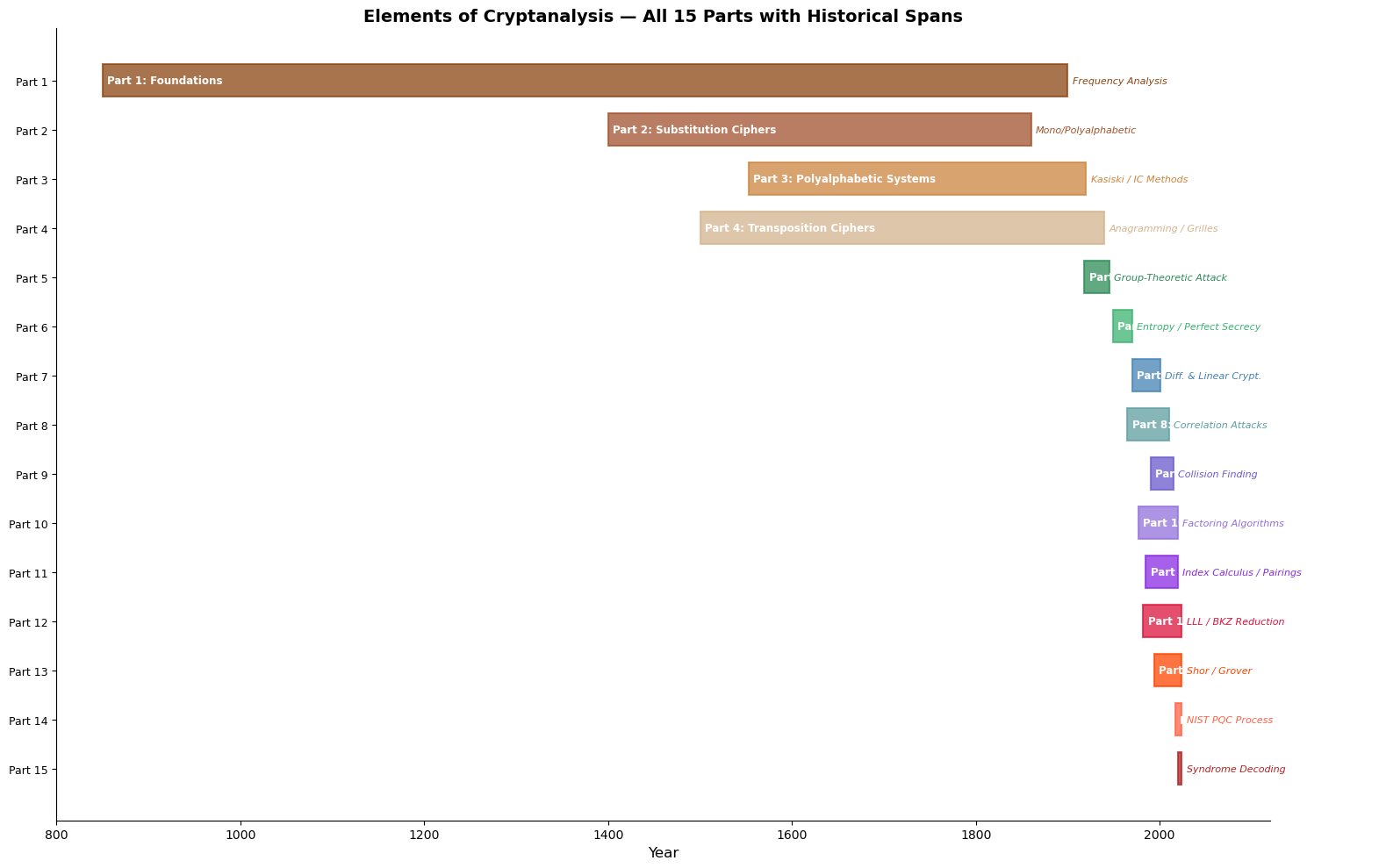
45.5 Summary of All 15 Parts#
The following table and visualisation summarise the full course structure, mapping each part to its key technique, approximate historical period, and primary impact on the field.
Show code cell source
import numpy as np
import matplotlib.pyplot as plt
# Full course summary data
parts = [
('Part 1', 'Foundations', 'Frequency Analysis', 850, 1900, '#8B4513'),
('Part 2', 'Substitution Ciphers', 'Mono/Polyalphabetic', 1400, 1860, '#A0522D'),
('Part 3', 'Polyalphabetic Systems', 'Kasiski / IC Methods', 1553, 1920, '#CD853F'),
('Part 4', 'Transposition Ciphers', 'Anagramming / Grilles', 1500, 1940, '#D2B48C'),
('Part 5', 'Rotor Machines', 'Group-Theoretic Attack', 1918, 1945, '#2E8B57'),
('Part 6', 'Shannon & Information Theory', 'Entropy / Perfect Secrecy', 1949, 1970, '#3CB371'),
('Part 7', 'Block Ciphers', 'Diff. & Linear Crypt.', 1970, 2001, '#4682B4'),
('Part 8', 'Stream Ciphers', 'Correlation Attacks', 1965, 2010, '#5F9EA0'),
('Part 9', 'Hash Functions', 'Collision Finding', 1990, 2015, '#6A5ACD'),
('Part 10', 'Public-Key: RSA', 'Factoring Algorithms', 1977, 2020, '#9370DB'),
('Part 11', 'Elliptic Curves', 'Index Calculus / Pairings', 1985, 2020, '#8A2BE2'),
('Part 12', 'Algebraic Cryptanalysis', 'Gröbner Bases / ANF', 2000, 2024, '#DC143C'),
('Part 13', 'The Quantum Threat', "Shor / Grover", 1994, 2024, '#FF4500'),
('Part 14', 'Lattice-Based Cryptography', 'LLL / BKZ Reduction', 1982, 2024, '#FF6347'),
('Part 15', 'Code-Based & Frontiers', 'Syndrome Decoding / PQC', 2017, 2024, '#B22222'),
]
fig, ax = plt.subplots(figsize=(16, 10))
for i, (part, title, technique, start, end, color) in enumerate(parts):
y = len(parts) - 1 - i
ax.barh(y, end - start, left=start, height=0.65, color=color,
alpha=0.75, edgecolor=color, linewidth=1.5)
ax.text(start + 5, y, f'{part}: {title}', va='center', fontsize=8.5,
fontweight='bold', color='white')
ax.text(end + 5, y, technique, va='center', fontsize=8, color=color,
fontstyle='italic')
ax.set_yticks(range(len(parts)))
ax.set_yticklabels([p[0] for p in parts][::-1], fontsize=9)
ax.set_xlabel('Year', fontsize=12)
ax.set_title('Elements of Cryptanalysis — All 15 Parts with Historical Spans',
fontsize=14, fontweight='bold')
ax.set_xlim(800, 2120)
ax.spines['top'].set_visible(False)
ax.spines['right'].set_visible(False)
plt.tight_layout()
plt.savefig('fig_ch45_all_parts.png', dpi=150, bbox_inches='tight')
plt.show()
Complete Course Summary Table#
Part |
Title |
Key Technique |
Period |
Impact |
|---|---|---|---|---|
1 |
Foundations |
Frequency analysis |
850–1900 |
Birth of cryptanalysis as a discipline |
2 |
Substitution Ciphers |
Mono/polyalphabetic analysis |
1400–1860 |
Broke centuries of “secure” communication |
3 |
Polyalphabetic Systems |
Kasiski / Index of Coincidence |
1553–1920 |
Defeated the “indecipherable” Vigenère |
4 |
Transposition Ciphers |
Anagramming, grille analysis |
1500–1940 |
Revealed permutation vulnerabilities |
5 |
Rotor Machines |
Group-theoretic cycle analysis |
1918–1945 |
Changed the course of World War II |
6 |
Shannon & Information Theory |
Entropy, unicity distance |
1949–1970 |
Put cryptography on rigorous foundations |
7 |
Block Ciphers |
Differential & linear cryptanalysis |
1970–2001 |
Shaped DES, led to AES design |
8 |
Stream Ciphers |
Correlation & algebraic attacks |
1965–2010 |
Secured wireless and real-time comm. |
9 |
Hash Functions |
Collision finding, length extension |
1990–2015 |
SHA-3 and sponge constructions |
10 |
Public-Key: RSA |
Factoring (NFS, ECM) |
1977–2020 |
Foundation of e-commerce security |
11 |
Elliptic Curves |
Index calculus, pairing attacks |
1985–2020 |
Efficient public-key at shorter key sizes |
12 |
Algebraic Cryptanalysis |
Gröbner bases, polynomial systems |
2000–2024 |
Algebraic modeling of ciphers over GF(2) |
13 |
The Quantum Threat |
Shor’s and Grover’s algorithms |
1994–2024 |
Existential threat to classical PKC |
14 |
Lattice-Based Cryptography |
LLL/BKZ basis reduction |
1982–2024 |
Leading post-quantum candidate family |
15 |
Code-Based Crypto & Frontiers |
Syndrome decoding, NIST PQC |
2017–2024 |
PQC standards and diversifying portfolio |
45.6 The Security#
Landscape: A Quantitative View
We now quantify how the effective security of different cryptographic families has evolved over time, accounting for both classical and quantum improvements in attacks.
Show code cell source
import numpy as np
import matplotlib.pyplot as plt
# Effective security (bits) of various 128-bit-target schemes over decades
decades = np.array([1970, 1980, 1990, 2000, 2010, 2020, 2030])
labels_decade = [str(y) for y in decades]
# Rough effective security trajectories
des_security = np.array([56, 56, 48, 42, 40, 38, 36])
rsa1024 = np.array([np.nan, 100, 90, 80, 73, 65, 0]) # broken by quantum ~2030s
aes128 = np.array([np.nan, np.nan, np.nan, 128, 128, 128, 128])
ecc256 = np.array([np.nan, np.nan, 128, 128, 128, 128, 0]) # broken by Shor
lattice256 = np.array([np.nan, np.nan, np.nan, np.nan, np.nan, 128, 120])
code_based = np.array([np.nan, np.nan, np.nan, np.nan, np.nan, 128, 125])
fig, ax = plt.subplots(figsize=(12, 7))
schemes = [
(des_security, 'DES (56-bit)', '#FF6347', 's'),
(rsa1024, 'RSA-1024', '#9370DB', 'o'),
(aes128, 'AES-128', '#4682B4', '^'),
(ecc256, 'ECC-256', '#2E8B57', 'D'),
(lattice256, 'Lattice-256', '#DC143C', 'P'),
(code_based, 'Code-Based', '#FF8C00', 'X'),
]
for data, label, color, marker in schemes:
mask = ~np.isnan(data)
ax.plot(decades[mask], data[mask], '-o', color=color, label=label,
marker=marker, markersize=8, linewidth=2, alpha=0.8)
ax.axhline(128, color='green', linestyle='--', linewidth=1, alpha=0.5)
ax.text(1972, 130, '128-bit target', fontsize=9, color='green')
ax.axhline(80, color='orange', linestyle='--', linewidth=1, alpha=0.5)
ax.text(1972, 82, '80-bit minimum (legacy)', fontsize=9, color='orange')
# Quantum era shading
ax.axvspan(2025, 2035, alpha=0.08, color='red')
ax.text(2027, 10, 'Quantum\nEra?', fontsize=10, color='red', fontstyle='italic')
ax.set_xlabel('Decade', fontsize=12)
ax.set_ylabel('Effective Security (bits)', fontsize=12)
ax.set_title('Evolution of Effective Security Across Cryptographic Families',
fontsize=13, fontweight='bold')
ax.legend(fontsize=9, loc='lower left')
ax.set_ylim(-5, 145)
ax.set_xlim(1965, 2035)
ax.spines['top'].set_visible(False)
ax.spines['right'].set_visible(False)
ax.grid(True, alpha=0.2)
plt.tight_layout()
plt.savefig('fig_ch45_security_evolution.png', dpi=150, bbox_inches='tight')
plt.show()
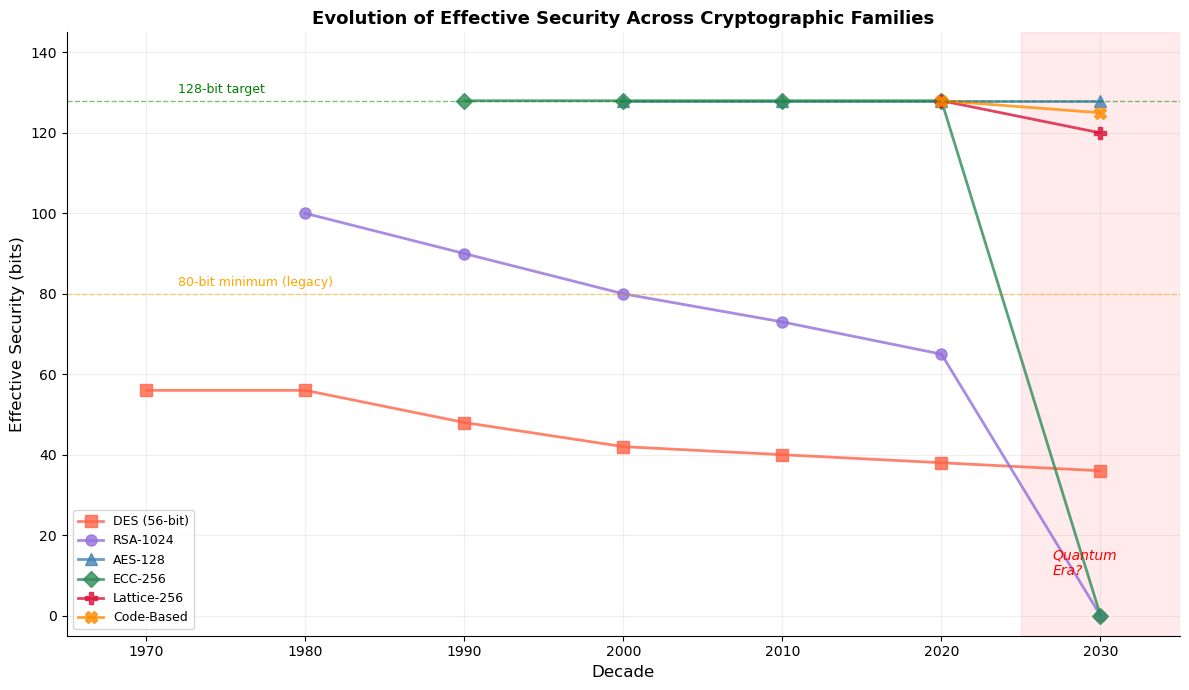
Interpreting the Security Evolution
The trajectories above are illustrative, not precise. The key message is that classical schemes degrade over time as attacks improve and hardware grows faster, while quantum-vulnerable schemes face a cliff-edge collapse. Post-quantum candidates (lattice, code-based) are designed to resist both classical and quantum attackers.
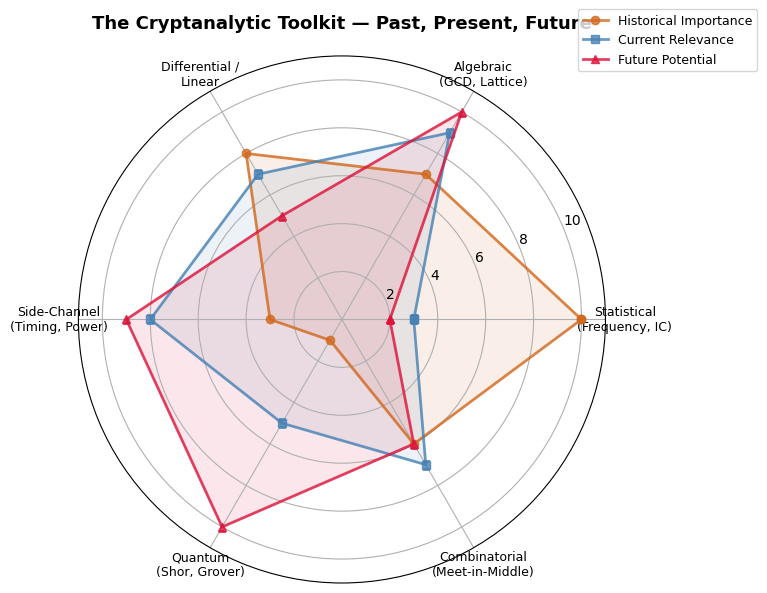
45.7 The Cryptanalytic Toolkit: A Taxonomy#
Over the course we have encountered dozens of attack techniques. The following radar chart groups them into six broad categories and estimates their relative importance in modern cryptanalysis.
Show code cell source
import numpy as np
import matplotlib.pyplot as plt
# Radar chart of attack families
categories = [
'Statistical\n(Frequency, IC)',
'Algebraic\n(GCD, Lattice)',
'Differential /\nLinear',
'Side-Channel\n(Timing, Power)',
'Quantum\n(Shor, Grover)',
'Combinatorial\n(Meet-in-Middle)',
]
N = len(categories)
# Scores: [historical importance, current relevance, future potential]
historical = [10, 7, 8, 3, 1, 6]
current = [3, 9, 7, 8, 5, 7]
future = [2, 10, 5, 9, 10, 6]
angles = np.linspace(0, 2 * np.pi, N, endpoint=False).tolist()
angles += angles[:1] # close the polygon
for data in [historical, current, future]:
data.append(data[0]) # close the polygon
fig, ax = plt.subplots(figsize=(8, 8), subplot_kw=dict(polar=True))
ax.plot(angles, historical, 'o-', color='#D2691E', linewidth=2,
label='Historical Importance', alpha=0.8)
ax.fill(angles, historical, color='#D2691E', alpha=0.1)
ax.plot(angles, current, 's-', color='#4682B4', linewidth=2,
label='Current Relevance', alpha=0.8)
ax.fill(angles, current, color='#4682B4', alpha=0.1)
ax.plot(angles, future, '^-', color='#DC143C', linewidth=2,
label='Future Potential', alpha=0.8)
ax.fill(angles, future, color='#DC143C', alpha=0.1)
ax.set_xticks(angles[:-1])
ax.set_xticklabels(categories, fontsize=9)
ax.set_ylim(0, 11)
ax.set_title('The Cryptanalytic Toolkit — Past, Present, Future',
fontsize=13, fontweight='bold', pad=20)
ax.legend(loc='upper right', bbox_to_anchor=(1.3, 1.1), fontsize=9)
plt.tight_layout()
plt.savefig('fig_ch45_toolkit_radar.png', dpi=150, bbox_inches='tight')
plt.show()
45.8 Lessons for the Practitioner#
From our survey, several practical lessons emerge:
Never rely on obscurity. Every proprietary cipher that has been analysed has been broken. Kerckhoffs’ principle (1883) remains paramount.
Understand your threat model. Classical, quantum, and side-channel attackers require different defences.
Crypto-agility is essential. Systems must be designed so that algorithms can be swapped without rebuilding the architecture.
Implementation matters as much as theory. Heartbleed, BEAST, and CRIME were all attacks on implementations, not on the underlying mathematics.
Diversity is a defence. Relying on a single hardness assumption (e.g., only lattices) is fragile. A portfolio approach — lattice, code-based, hash-based — provides resilience.
Show code cell source
import numpy as np
import matplotlib.pyplot as plt
# Final visualisation: the "health" of major cryptographic families
families = [
'Symmetric\n(AES, ChaCha)',
'RSA / DH /\nDSA',
'Elliptic\nCurves',
'Lattice-Based\n(Kyber, Dilithium)',
'Code-Based\n(Classic McEliece)',
'Hash-Based\n(SPHINCS+)',
]
# Scores on classical security, quantum security, maturity, efficiency
classical_sec = np.array([10, 7, 9, 9, 8, 10])
quantum_sec = np.array([7, 0, 0, 8, 8, 10]) # Grover halves symmetric
maturity = np.array([10, 10, 9, 6, 5, 7])
efficiency = np.array([10, 5, 8, 7, 3, 4])
x = np.arange(len(families))
width = 0.2
fig, ax = plt.subplots(figsize=(14, 7))
ax.bar(x - 1.5*width, classical_sec, width, label='Classical Security',
color='#4682B4', alpha=0.8)
ax.bar(x - 0.5*width, quantum_sec, width, label='Quantum Security',
color='#DC143C', alpha=0.8)
ax.bar(x + 0.5*width, maturity, width, label='Maturity',
color='#2E8B57', alpha=0.8)
ax.bar(x + 1.5*width, efficiency, width, label='Efficiency',
color='#FF8C00', alpha=0.8)
ax.set_xticks(x)
ax.set_xticklabels(families, fontsize=9)
ax.set_ylabel('Score (0–10)', fontsize=11)
ax.set_title('Cryptographic Family Health Report — 2024',
fontsize=13, fontweight='bold')
ax.legend(fontsize=9, loc='upper right')
ax.set_ylim(0, 12)
ax.spines['top'].set_visible(False)
ax.spines['right'].set_visible(False)
plt.tight_layout()
plt.savefig('fig_ch45_health_report.png', dpi=150, bbox_inches='tight')
plt.show()
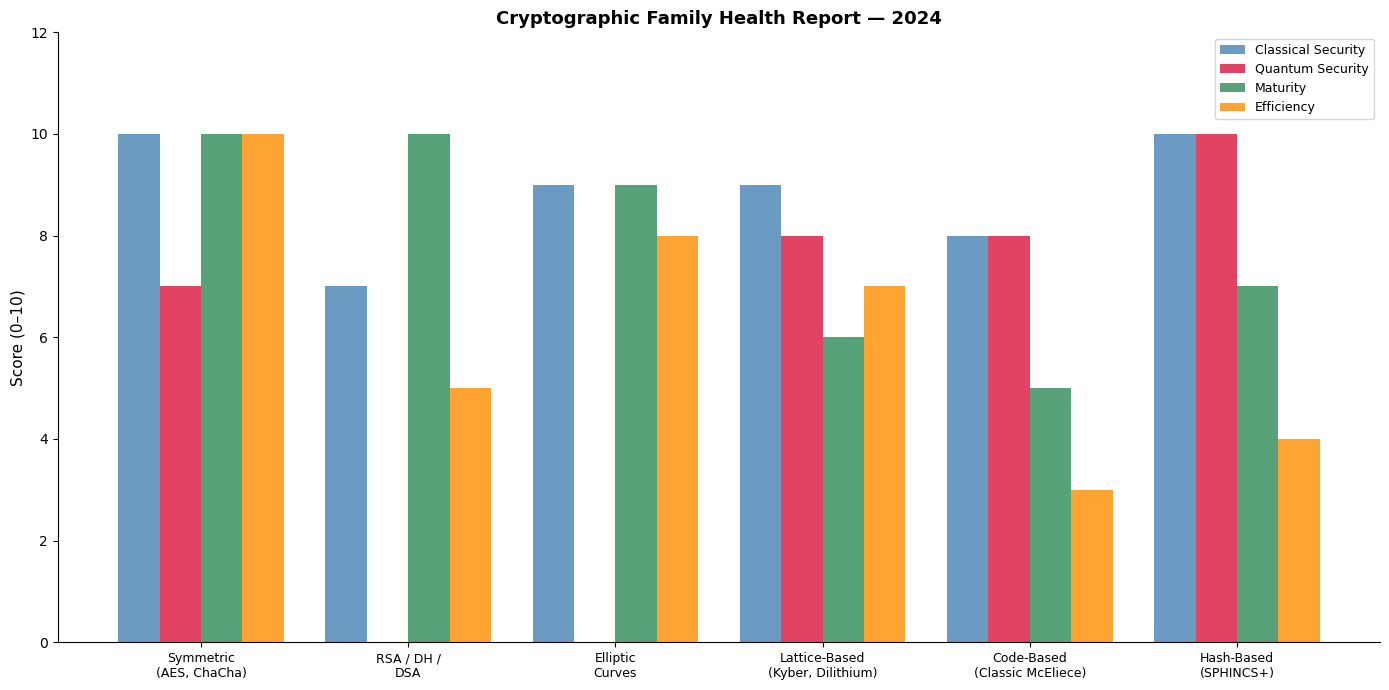
The Portfolio Approach
No single post-quantum family excels in all dimensions. NIST’s decision to standardise schemes from multiple families (lattice-based Kyber/Dilithium alongside hash-based SPHINCS+ and code-based candidates) reflects the wisdom of diversification — precisely because our confidence in any single hardness assumption is necessarily limited.
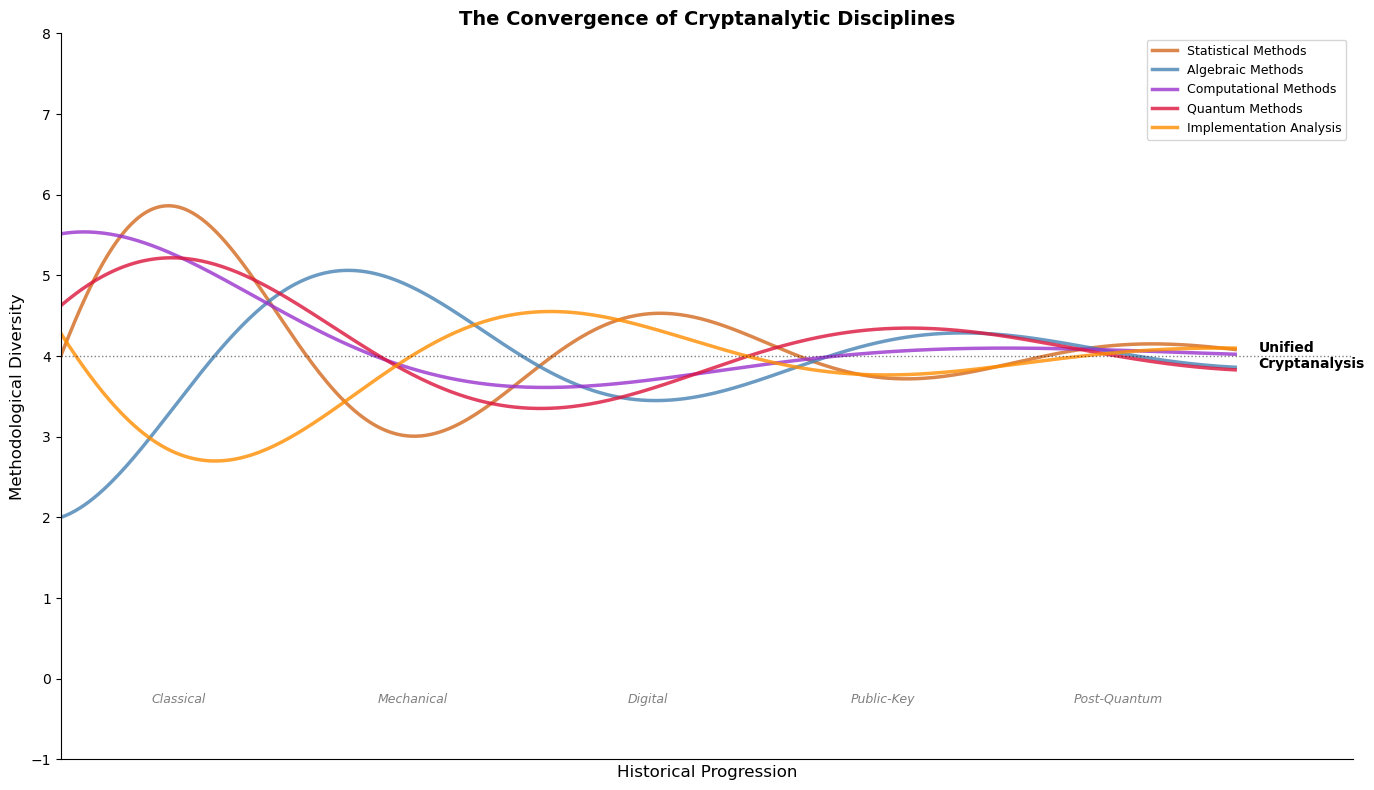
45.9 Concluding Reflections on the Future of Cryptography#
As we close this course, several forward-looking observations are worth recording.
The transition to post-quantum cryptography is underway. NIST has published its first post-quantum standards. The migration of the global internet to these new algorithms is a multi-decade infrastructure project comparable in scale to the transition from HTTP to HTTPS.
Cryptanalysis will continue to surprise us. The 2022 break of SIDH/SIKE — a leading isogeny-based candidate — by Castryck and Decru demonstrated that even well-studied schemes can fall to unexpected mathematical insights. Vigilance and scepticism remain the cryptanalyst’s chief virtues.
The interplay of theory and practice deepens. Formal verification, constant-time programming, and hardware-software co-design are becoming as important as the mathematical theory of the underlying algorithms. The cryptanalyst of the future must be as comfortable reading assembly code as proving theorems.
AI-assisted cryptanalysis is emerging. Machine learning techniques are beginning to be applied to cipher analysis, side-channel attacks, and protocol verification. Whether AI will produce fundamentally new attack paradigms — or merely accelerate existing ones — remains to be seen.
The human element persists. Despite all mathematical and computational advances, the weakest link in most cryptographic systems remains the human user. Social engineering, key mismanagement, and implementation errors continue to dominate real-world breaches.
Show code cell source
import numpy as np
import matplotlib.pyplot as plt
# Final figure: a "convergence" plot showing how different threads
# of cryptanalysis converge toward a unified discipline
fig, ax = plt.subplots(figsize=(14, 8))
# Time axis
t = np.linspace(0, 10, 500)
# Threads that converge
threads = [
('Statistical Methods', lambda t: 4 + 2.5 * np.exp(-0.3 * t) * np.sin(1.5 * t)),
('Algebraic Methods', lambda t: 4 - 2.0 * np.exp(-0.25 * t) * np.cos(1.2 * t)),
('Computational Methods', lambda t: 4 + 1.8 * np.exp(-0.35 * t) * np.sin(0.8 * t + 1)),
('Quantum Methods', lambda t: 4 - 1.5 * np.exp(-0.2 * t) * np.cos(1.0 * t + 2)),
('Implementation Analysis', lambda t: 4 + 2.0 * np.exp(-0.3 * t) * np.sin(1.1 * t + 3)),
]
colours = ['#D2691E', '#4682B4', '#9932CC', '#DC143C', '#FF8C00']
for (name, func), color in zip(threads, colours):
y = func(t)
ax.plot(t, y, linewidth=2.5, color=color, label=name, alpha=0.8)
# Convergence target line
ax.axhline(4, color='black', linestyle=':', linewidth=1, alpha=0.5)
ax.text(10.2, 4, 'Unified\nCryptanalysis', fontsize=10, va='center',
fontweight='bold', color='black')
# Era labels on x-axis
era_labels = [
(1.0, 'Classical'),
(3.0, 'Mechanical'),
(5.0, 'Digital'),
(7.0, 'Public-Key'),
(9.0, 'Post-Quantum'),
]
for x, label in era_labels:
ax.text(x, -0.3, label, ha='center', fontsize=9, fontstyle='italic',
color='grey')
ax.set_xlim(0, 11)
ax.set_ylim(-1, 8)
ax.set_xlabel('Historical Progression', fontsize=12)
ax.set_ylabel('Methodological Diversity', fontsize=12)
ax.set_title('The Convergence of Cryptanalytic Disciplines',
fontsize=14, fontweight='bold')
ax.legend(loc='upper right', fontsize=9)
ax.set_xticks([])
ax.spines['top'].set_visible(False)
ax.spines['right'].set_visible(False)
plt.tight_layout()
plt.savefig('fig_ch45_convergence.png', dpi=150, bbox_inches='tight')
plt.show()
A Final Word
Cryptanalysis is not merely the art of breaking ciphers. It is a discipline that compels us to think rigorously about what it means for a system to be secure, to distinguish genuine confidence from false assurance, and to remain perpetually humble before the ingenuity of future adversaries. The journey from Al-Kindi to post-quantum cryptography is, at its deepest level, a journey in the philosophy of knowledge — what can be known, what can be hidden, and what remains forever uncertain.
Exercises#
Timeline Extension: Add at least five additional events to the timeline visualisation from Section 45.1. Research events not covered in the course (e.g., the Venona project, the BEAST attack, the Snowden revelations).
Dialectic Analysis: Identify a cipher-attack-response triple not listed in Section 45.2. Describe the cipher, the attack that broke it, and the stronger cipher that resulted.
Open Problem Report: Choose one open problem from Section 45.4 and write a 500-word summary of the current state of research, citing at least three recent papers.
Comparative Essay: Compare the NIST post-quantum standardisation process (2017–2024) with the AES competition (1997–2001). What lessons were learned? What new challenges arose?
Future Scenario: Write a speculative but technically grounded scenario for cryptography in 2050. What hardness assumptions might remain standing? What new attack paradigms might have emerged?
Chapter Summary#
This final chapter has synthesised the arc of Elements of Cryptanalysis across its 15 parts and 45 chapters. The key takeaways are:
Cryptanalysis has evolved from frequency counting to quantum algorithm design, but the fundamental dialectic — cipher, attack, stronger cipher — has remained constant.
Four grand themes structure the field: statistical analysis, algebraic structure, computational hardness, and quantum threats.
Significant open problems remain, from the foundations of complexity theory to the practical security of lattice-based schemes.
The future demands a unified approach that combines mathematical theory, implementation security, and crypto-agile system design.
The study of cryptanalysis is never truly complete — as long as there are secrets worth protecting, there will be adversaries seeking to uncover them, and defenders working to stay one step ahead.
Further Reading#
Katz, J. and Lindell, Y. (2020). Introduction to Modern Cryptography. 3rd edition. CRC Press.
Singh, S. (1999). The Code Book. Anchor Books.
Bernstein, D.J. and Lange, T. (2017). “Post-quantum cryptography.” Nature, 549, 188–194.
NIST (2024). Post-Quantum Cryptography Standardization. https://csrc.nist.gov/projects/post-quantum-cryptography
Boneh, D. and Shoup, V. (2020). A Graduate Course in Applied Cryptography. Online textbook.
